
The majority of attacks in 2018 were aimed at direct financial profit or obtaining sensitive information, according to PT Security’s Cybersecurity Threatscape 2018 Report. However, attacks aimed at data theft often have financial implications: Data can be used for stealing money, blackmailing, and can even be sold on the darkweb.
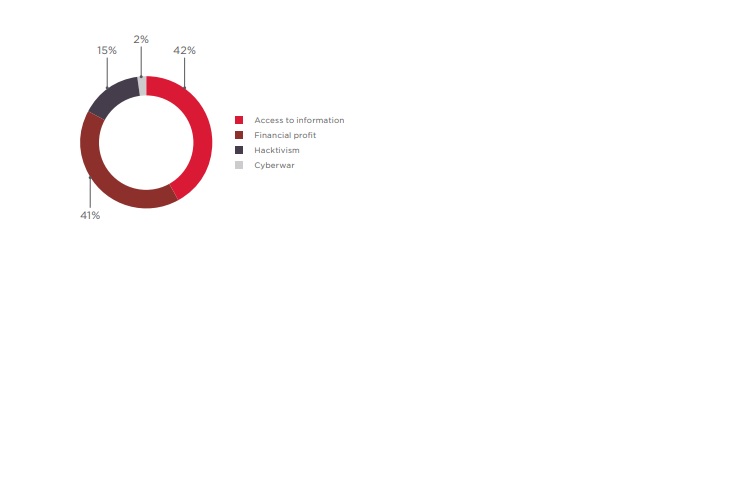
Figure 1: Attackers' motives
Unlike 2017, most attacks were targeted (55%), with their share growing gradually from quarter to quarter. Almost a quarter of attacks (23%) hit individuals. As for organizations, government institutions suffered in 19% of cases, whereas healthcare and financial institutions were targeted in 11 and 10% of cases, respectively. Large-scale cyberattacks affecting more than one industry have been placed in the "Multiple industries" category.
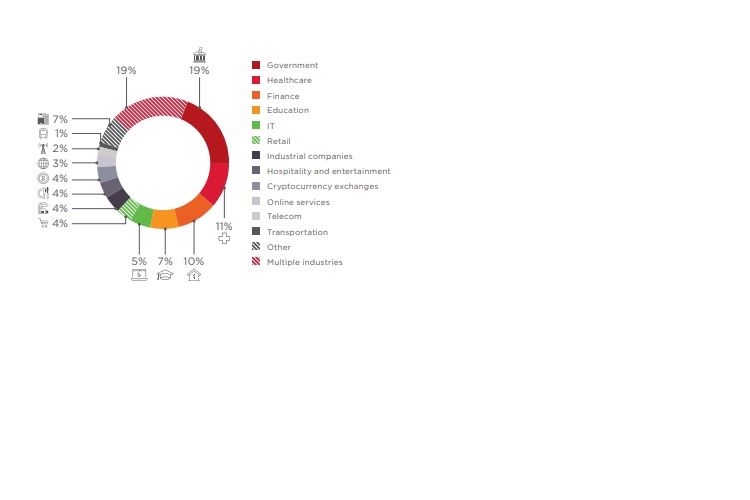
Figure 2: Victim Categories among Organizations
In 2018, the number of unique incidents grew by 27% compared to the previous year. No significant declines in hacker activity were seen during the year. Attacker activity was at its peak in February, May, July, and at the end of the year, which can be linked to major sports competitions (Winter Olympic Games and FIFA World Cup), as well as the winter holiday season, when both individuals and companies tend to be more active financially.
The percentage of targets changed only minimally compared to 2017. In most cases, attackers hit corporate infrastructure (49%) and websites (26%). The share of attacks on POS terminals and ATMs decreased from 3 to 1%.
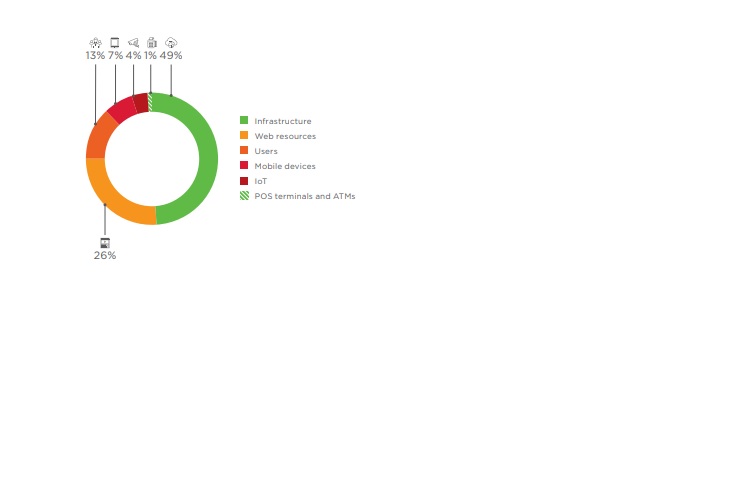
Figure 3: Attack Targets
Attacks are becoming more and more sophisticated, and often consist of several stages with different methods used. Malware was used in more than half of attacks. Every third attack involved social engineering.
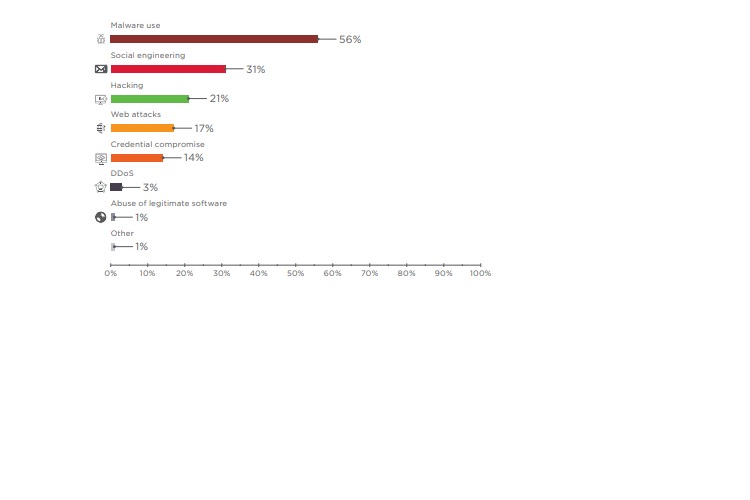
Figure 4: Attack Methods
Threats encountered by various sectors in 2018
Government
Attacks were mostly driven by theft of sensitive information, which accounted for 51% of cases. Government websites are often targeted as a way to draw public attention: Hacktivist attacks accounted for approximately a quarter of all incidents. In most cases, hackers attacked government infrastructure and infected computers with spyware and remote administration malware. Over 20 ransomware campaigns against government institutions were recorded in 2018. Attackers made extensive use of social engineering to penetrate internal networks: Malware was distributed via official app stores, sent by email, and even delivered on CDs by ordinary post. In Q1, Positive Technologies Expert Security Center (PT ESC) experts discovered phishing emails distributing an updated version of SANNY spyware and the Fucobha Trojan. The end of the year was marked by attacks by the Treasure Hunters, Danti APT, and SongXY groups, which sent malicious documents to government institutions in Russia and the CIS.
Healthcare
In 2018, hackers showed increased interest in healthcare institutions. The number of attacks against healthcare was even higher than that against the financial sector. Attackers got hold of personal data and medical information of more than 6 million people. Hackers hunt for data but also for quick profits, knowing that uninterrupted system operation is key when patients' lives are at stake. Attackers penetrated the infrastructure of medical institutions, encrypted data, and then demanded a ransom for restoring the systems. For example, Hancock Regional Hospital in the US paid hackers USD 55,000 to regain use of its computer systems.
Finance
In most attacks against financial institutions, hackers were driven by direct financial profit (65% of incidents). All the same, stealing payment card information, personal data, and account credentials also accounted for a large share of incidents. Criminals can use this data to steal money from people's accounts or sell it on the darkweb. The beginning of 2018 saw a surge of jackpotting attacks in the US, with criminals installing Ploutus-D malware on ATMs to empty them of cash. Interestingly, the fraudsters used medical endoscopes to emulate physical authentication without access to the ATM's safe. The second half of 2018 was marked by attacks from known APT groups. PT ESC experts recorded 23 attacks by the Cobalt group. The criminals created new malware and distributed it in emails seemingly originating from trusted financial institutions. In addition, the experts discovered a new group attacking the finance sector. The malefactors sent malicious documents with macros that downloaded utilities providing remote access to infected computers. Phishing messages were sent from a compromised mailbox of an employee of a major financial company. In another case, they were disguised as coming from a government cybersecurity authority. A modified script earlier used by Treasure Hunters was uncovered in the documents. However, further analysis of traffic and the utilities used by the attackers indicated the emergence of a new criminal group.
Education
By and large, criminals stole personal data of employees and students, as well as credentials used for email, bank accounts, and other services. At several educational institutions, attackers accessed bank accounts and payment documents, stealing over USD 2 million in total. Every sixth attack involved ransomware. Hackers either demanded a ransom to restore data or simply wanted to paralyze the computer systems of educational institutions. Q2, which marks the end of the academic year, saw an increasing number of attacks aimed at changing grades in virtual student records. Attempting to steal intellectual property, such as scientific work and unpublished research, hackers attacked scientific institutes. This information is often sought by government-sponsored hacker groups. Several such attacks were attributed to hackers in Iran and North Korea. Malefactors also cash in by publishing stolen research on attacker-controlled websites that users must pay to access.
IT
Hackers attacked websites and infrastructure of IT companies. Oftentimes, such hacks are just intermediate links in more complex attacks. The servers of IT companies may store confidential client information. In the case of service providers, these systems hold data belonging to other companies, including those companies' websites. Hackers also seek to gain access to corporate email accounts in order to use them for phishing attacks. Websites of prominent software developers have become a convenient platform for distributing malware under the guise of official updates. In Q2, PT ESC experts detected a phishing attack aimed at a major IT company: The PlugX Trojan was distributed via corporate email. The Trojan has been used by attackers for years as spyware. IT companies were the second-most common target of DDoS attacks, after government institutions. Hackers disrupted the operations of internet service providers and game companies, which are particularly sensitive to downtime and equipment disruption.
Retail
Online stores were a favorite target of attacks aimed at data theft. In 70% of cases, payment card information was stolen. The second part of the year was marked by attacks conducted by the Magecart group. Hackers injected malicious scripts into web applications in order to collect payment information and contact data entered by users. The number of attacks against POS terminals decreased by two thirds compared to 2017. However, POS terminals were still hit hard in one of the biggest retail attacks. Hackers installed malware on POS terminals located in Saks Fifth Avenue and Lord & Taylor stores and stole data for more than 5 million cards.
Hospitality and Entertainment
In this sector, attacks were mainly aimed at stealing client data, especially payment card information. Many incidents involved installing malware on POS terminals. A massive data leak happened in 2018 as a result of a cyberattack on the Marriott hotel chain. Hackers stole personal information for 383 million guests, including passport and payment card information. Marriott stock fell 6% in one day and kept falling for another two weeks.

 In
In
Comments
Acquisto Viagra Generico In
Acquisto Viagra Generico In Italia https://ascialis.com/ - Cialis Purchasing Viagra In Canada <a href=https://ascialis.com/#>Cialis</a> Saint
Acquisto Viagra Generico In
Acquisto Viagra Generico In Italia https://ascialis.com/ - Cialis Purchasing Viagra In Canada <a href=https://ascialis.com/#>Cialis</a> Saint
Acquisto Viagra Generico In
Acquisto Viagra Generico In Italia https://ascialis.com/ - Cialis Purchasing Viagra In Canada <a href=https://ascialis.com/#>Cialis</a> Saint
Acquisto Viagra Generico In
Acquisto Viagra Generico In Italia https://ascialis.com/ - Cialis Purchasing Viagra In Canada <a href=https://ascialis.com/#>Cialis</a> Saint
buy viagra in italy
buy viagra in italy
[url=https://deliveryviagranow.com/]viagra online[/url]
<a href="https://deliveryviagranow.com/">coste de viagra canad</a>
argentina free viagra
buy viagra in italy
buy viagra in italy
[url=https://deliveryviagranow.com/]viagra online[/url]
<a href="https://deliveryviagranow.com/">coste de viagra canad</a>
argentina free viagra
Add new comment