
37% organizations have been affected by cryptominers globally, followed by mobile malware (33%), botnet malware (18%), banking malware (13%) and ransomware (4%), according to Checkpoint’s Cyber Attack Trends Analysis Security Report 2019.
The report indicates although there is rise in cryptomining attacks, there is a sharp decline in the ransomware attacks. (See Figure 1)
Figure 1: Top cyber attack categories globally and by region
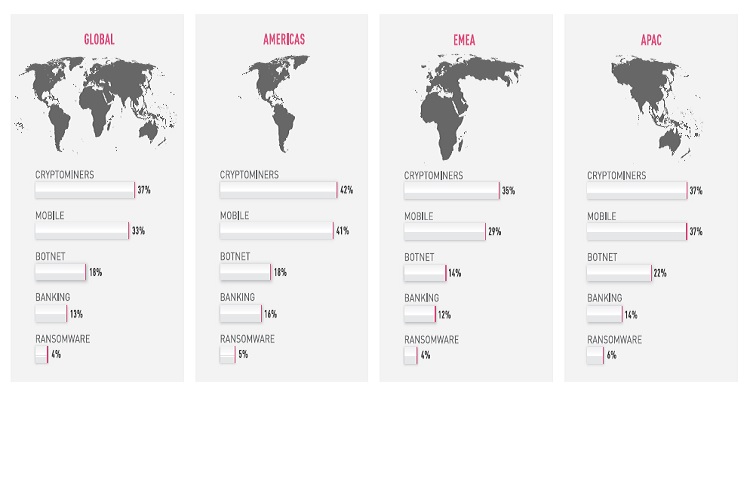
Source: Checkpoint’s Cyber Attack Trends Analysis Security Report 2019
Checkpoint outlines key cyber threats which affected organizations globally in 2018:
Crytominers dominated the malware landscape in 2018
Cryptomining attacks soared in 2018, affecting over 40% of organizations worldwide at its peak, compared to 20.5% at the end of 2017, and dominated the top cyberattacks and malware families. In January 2018, total cryptocurrency values dropped rapidly, shrinking by about 86% from their peak. Despite this, cryptominers detached themselves from cryptocurrencies’ market cap and kept their place as the most prominent malware infection used by threat actors in 2018. A year after they took the world by storm, cryptominers show no intention of slowing down soon. New, sophisticated malware families keep integrating mining capabilities to their code and tens of thousands of websites are constantly compromised to exploit their users’ resources.
Mobiles are a moving target
33% of organizations worldwide were hit by mobile malware, with the leading three malware types targeting the Android OS. 2018 saw several cases where mobile malware was pre-installed on devices, and apps available from app stores that were actually malware in disguise.
Hiddad, an ad-distributing malware for Android that can bypass the Google Play Protect verification system, is back in the top ranks as the top mobile malware globally, as well as in the APAC and EMEA. This year Hiddad presented various persistence techniques along with camouflage methods, which made it one of the most prominent mobile malware. Guerilla is a new mobile malware family which is embedded in multiple legitimate apps and can download additional malicious payloads to generate fraudulent ad revenue.
Multi-purpose botnets launch range of attacks
Bots were the third most common malware type, with 18% of organizations hit by bots which are used to launch DDoS attacks and spread other malware. Bot infections were instrumental in nearly half (49%) of organizations experiencing a DDoS attack in 2018.
The notorious Necurs, which first emerged in 2012, is at the head of the top global, Americas and EMEA ranks, and is one of the most prevalent botnets of 2018. This year, the giant spam botnet adopted new techniques to avoid detection, targeted banks, was behind a variety of email scams, and pushed various payloads including cryptominers, ransomware, banking Trojans, and RATs. Due to its massive distribution size, ‘Necurs’ was single-handedly responsible for the steep rise observed in URL file type, using it to trick victims into clicking and downloading an additional malware. Dorkbot is another prominent botnet which dominated the charts. It reached the top of APAC ranks, and also ranked second in the EMEA and globally. Dorkbot, the known modular bot which functions mainly as a downloader or as a launcher for other binary components, was observed this year utilizing an array of AntiVM and persistence techniques, as well as APC-Injection which allows it to inject malicious code into a legitimate process in a very early stage of thread initialization, thus avoiding detection.
Banks still not spared
13% organizations have been affected by banking malware in 2018. Ramnit is the most prominent banking Trojan of the past year. It first appeared in 2010 and has remained active ever since. Ramnit’s popularity is in line with the exposure by Check Point researchers of a massive new ‘Black’ campaign based on the banker. The campaign turned the victim machines into malicious proxy servers and resulted in over 100,000 infections. Shortly after the ‘Black’ campaign was shut down, a new Ramnit campaign emerged, distributing the AZORult info-stealer and downloader, via the RIG and GrandSoft Exploit Kits. Trickbot is another dominant banking Trojan widely observed in 2018 that reached the top of the global, Americas and EMEA rankings. As an advanced malware based on plugins, Trickbot is constantly being updated with new capabilities, features and distribution vectors. This enables Trickbot to be a flexible and customizable malware that can be distributed as part of multipurposed campaigns. This year we witnessed TrickBot being delivered via multiple global spam campaigns, as well as creatively cooperating and sharing profits with the IcedID banking malware.
Ransomware attacks in decline
2018 saw ransomware usage fall sharply, impacting just 4% of organizations globally. This is down from 30% in 2017. This shift may be the result of the move to cryptomining as a more efficient and profitable alternative. It can also be related to the adoption of the ‘boutique’ ransomware attacks that only target specific organizations instead of wide global campaigns.
“From the meteoric rise in cryptomining to massive data breaches and DDoS attacks, there was no shortage of cyber-disruption caused to global organizations over the past year. Threat actors have a wide range of options available to target and extract revenues from organizations in any sector, and the first instalment of the 2019 Security Report highlights the increasingly stealthy approaches they are currently using,” says Peter Alexander, Chief Marketing Officer of Check Point Software Technologies. “These multi-vector, fast-moving, large-scale Gen V attacks are becoming more and more frequent, and organizations need to adopt a multi-layered cybersecurity strategy that prevents these attacks from taking hold of their networks and data. The 2019 Security Report offers knowledge, insights and recommendations on how to prevent these attacks.”

 In
In
Comments
Viagra Rezeptfrei Bankeinzug
Viagra Rezeptfrei Bankeinzug https://buycialisuss.com/ - Cialis wholesale cialis <a href=https://buycialisuss.com/#>Cialis</a> buy levitra now
Add new comment