
Account takeover (ATO) attacks, in which a person's credentials are stolen and used to send emails from their real account, have multiple objectives. Some attackers try to use the hacked email account to launch phishing campaigns that will go undetected, some attackers steal credentials of other employees and sell them in the black market, and others use the account to conduct reconnaissance to launch personalized attacks. The most sophisticated attackers steal the credentials of a key employee (e.g., CEO or CFO), and use them to launch a Business Email Compromise attack from the real employee's email address.
To better understand the extent of account takeover, Grant Ho, along with the Barracuda Sentinel team, ran a study on 50 randomly selected organizations. These organizations span different sectors, including private companies, public organizations, and educational institutions. These organizations reported account takeover incidents to us over a three month period, from the beginning of April until the end of June 2018. Note that this study may underestimate the number of real account takeover incidents, since some incidents may have taken place without the organization's knowledge.
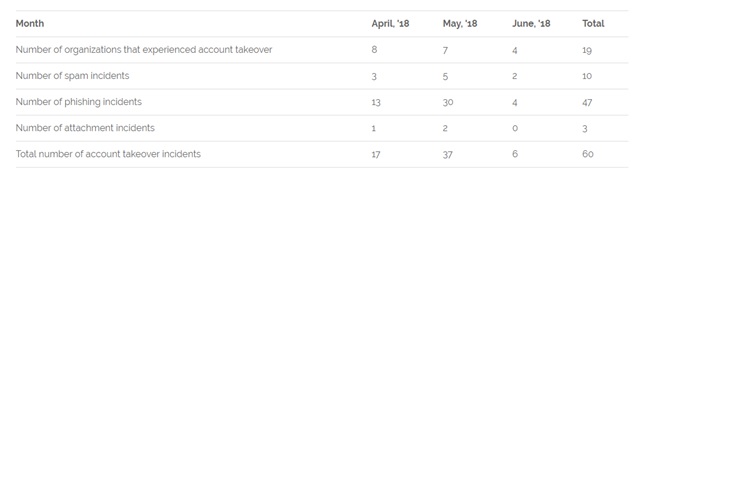
The above table includes a summary of the incidents reported by these organizations. An account takeover incident is defined as an employee's email being used by an attacker to email other people, either internal employees or external parties.
Overall, in each month 4-8 organizations reported at least one account takeover incident, and the total number of incidents reported was 60. On average, when a company got compromised, the compromise resulted in at least 3 separate account takeover incidents, where either the same or different employees accounts were used for nefarious purposes. Out of the 60 incidents, 78% resulted in a phishing email. In these phishing emails, the goal of the attacker was typically to infect additional internal and external accounts. The email usually impersonates the employee and asks the recipient to click on a link. Another 17% of incidents were used as platforms for sending spam campaigns. The reason attackers love using compromised accounts as vehicles for launching spam is that the accounts often have very high reputations: They are coming from reputable domains, from the correct IP, and from real people that have a legitimate email history. Therefore, they are much likely to get blocked by email security systems that rely on domain, sender or IP reputation. Finally, 5% of incidents involved in the attacker asking the recipient to download an attachment. These incidents all involved internal email traffic. This attack is effective because most email security systems do not scan internal traffic for threats. Therefore, attackers can send malware with relative ease internally, and the recipients will often open the attachments, which will cause their endpoints to get infected.
Barracuda Sentinel is the only solution in the market that can automatically prevent email account takeover. It combines three powerful layers: an AI engine that stops spear phishing attacks in real time, including emails that originate from within the company; domain fraud visibility using DMARC authentication to guard against domain spoofing and brand hijacking and fraud simulation training for high-risk individuals. Employees should be trained to increase security awareness of various attacks. Simulated attack training is the most effective form of training. Barracuda PhishLine provides comprehensive, SCORM-compliant user training and testing as well as phishing simulation for emails, voicemail, and SMS along with other helpful tools to train users to identify cyberattacks.

 In
In
Comments
Amoxicillin And Vitamin
Amoxicillin And Vitamin https://bbuycialisss.com/ - Buy Cialis Effet Du Cialis Generique <a href=https://bbuycialisss.com/#>buy cialis online without a prescription</a> Macrobid Best Buy Overseas Free Consultation
Amoxicillin And Vitamin
Amoxicillin And Vitamin https://bbuycialisss.com/ - Buy Cialis Effet Du Cialis Generique <a href=https://bbuycialisss.com/#>buy cialis online without a prescription</a> Macrobid Best Buy Overseas Free Consultation
Amoxicillin And Vitamin
Amoxicillin And Vitamin https://bbuycialisss.com/ - Buy Cialis Effet Du Cialis Generique <a href=https://bbuycialisss.com/#>buy cialis online without a prescription</a> Macrobid Best Buy Overseas Free Consultation
Amoxicillin And Vitamin
Amoxicillin And Vitamin https://bbuycialisss.com/ - Buy Cialis Effet Du Cialis Generique <a href=https://bbuycialisss.com/#>buy cialis online without a prescription</a> Macrobid Best Buy Overseas Free Consultation
Add new comment