
With the govt’s push for creating a cashless economy by empowering all users with digital apps, Aadhaar linking with Bank accounts, we are creating new vulnerabilities for exploitation by hackers
'IT Security’ and Internet of Things (IoT) are of great significance in today’s digitally connected world. The rapid pace of getting everything connected and online in a “smart” world is creating new vulnerabilities that can be exploited by hackers. Ransomware as a concept has been around for years now but has recently evolved. Hacking group, 'The Shadow Brokers', was behind the WannaCry Ransomware outbreak which used unpatched OS level vulnerabilities originally discovered by another “grey” group, “The Equation Group”, which according to speculation is associated with the US National Security Agency.
It is speculated that the NSA-backed “Shadow Brokers” actually pays software conglomerates to NOT patch the vulnerabilities discovered in their software until they are revealed publicly. This is to allow US agencies in their clandestine espionage activities against other countries using the software. It is a well-known fact that Microsoft patched the SMB vulnerability in March 2017 only when the exploit was already published in February, on the Dark Web and Internet.
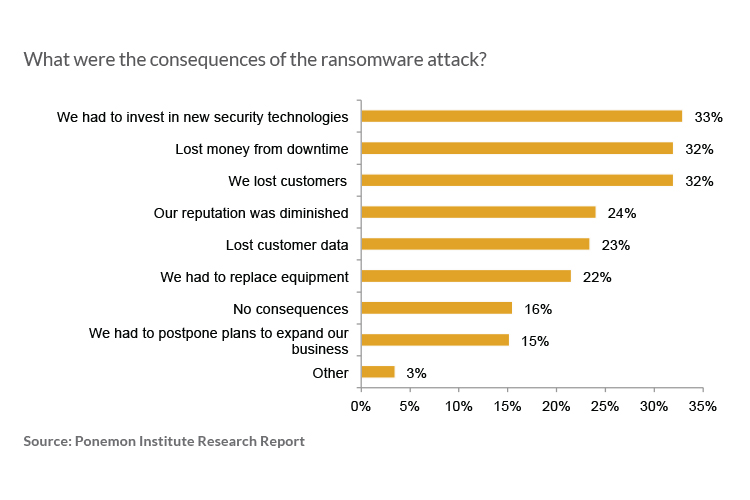
Ransomware attacks were predicted to cost an aggregate of USD 5 billion in 2017 alone. Soon after WannaCry in June 2017, another Ransomware Petya crippled Fortune 500 Shipping company, Maersk Lines, when their systems were affected for days leading to estimated losses of USD 300 million.
With the governments push for creating a cashless economy by empowering all users with digital apps, Aadhaar linking with bank accounts, OTP-based two-facto authentication, we are also creating new vulnerabilities for exploitation by hackers.
Consider the scenario where a ransomware encrypts our data and demands a ransom for decryption keys. Such malicious software can sneak into our smartphones in the guise of an app and get permission to access messages and reply to the messages in an automated fashion.
Even today, there are “applications” designed to “read” and capture “OTPs” sent by banks and submit to e-commerce sites for validating our online transactions; the only user interaction required is a click on the “Submit” button. Some users inadvertently save their credit/debit card data on their phone's memory for auto-populating the various fields in the online transaction screen. This leaves the user exposed to such malicious e-robbers who can wipe out your bank accounts after reading, misusing and deleting the OTP message stealthily.
User awareness is the key to protect against such e-robbery, such as, using virtual credit card numbers with fixed denomination approved namely, Netsafe which is provided by HDFC Bank etc.. These one-time use CC/DC numbers cannot be misused even if known to someone after the first-use. The recent steps by RBI to make it mandatory for banks and NBFCs to report security breaches is a welcome step which puts the banks’ processes under scanner and will force them to revisit, re-analyze, and strengthen their online financial processes.

 In
In
Comments
Il Viagra Sulle Donne https:
Il Viagra Sulle Donne https://bbuycialisss.com/ - buy viagra cialis online Comprare Cialis Svizzera <a href=https://bbuycialisss.com/#>Cialis</a> Propecia Canadian Cialis Soft
Il Viagra Sulle Donne [url
Il Viagra Sulle Donne [url=https://bbuycialisss.com/]buy viagra cialis online[/url] Comprare Cialis Svizzera <a href=https://bbuycialisss.com/#>Cialis</a> Propecia Canadian Cialis Soft
Add new comment